Why Your Compliance Posture Drifts Between Audits
Every compliance team knows the rhythm.
Eight weeks before the audit, preparation begins. Evidence is collected. Controls are reviewed. Gaps are identified and remediated. Policy documents are updated. Attestations are gathered. By the time the auditor arrives, the organization's compliance posture looks comprehensive, current, and well-maintained.
Two weeks after the audit, the drift begins.
A new workflow is deployed without a corresponding policy update. A team restructures and control ownership shifts without documentation. An exception is granted for a production incident and never reverted. A vendor changes their security posture and the third-party risk assessment isn't refreshed.
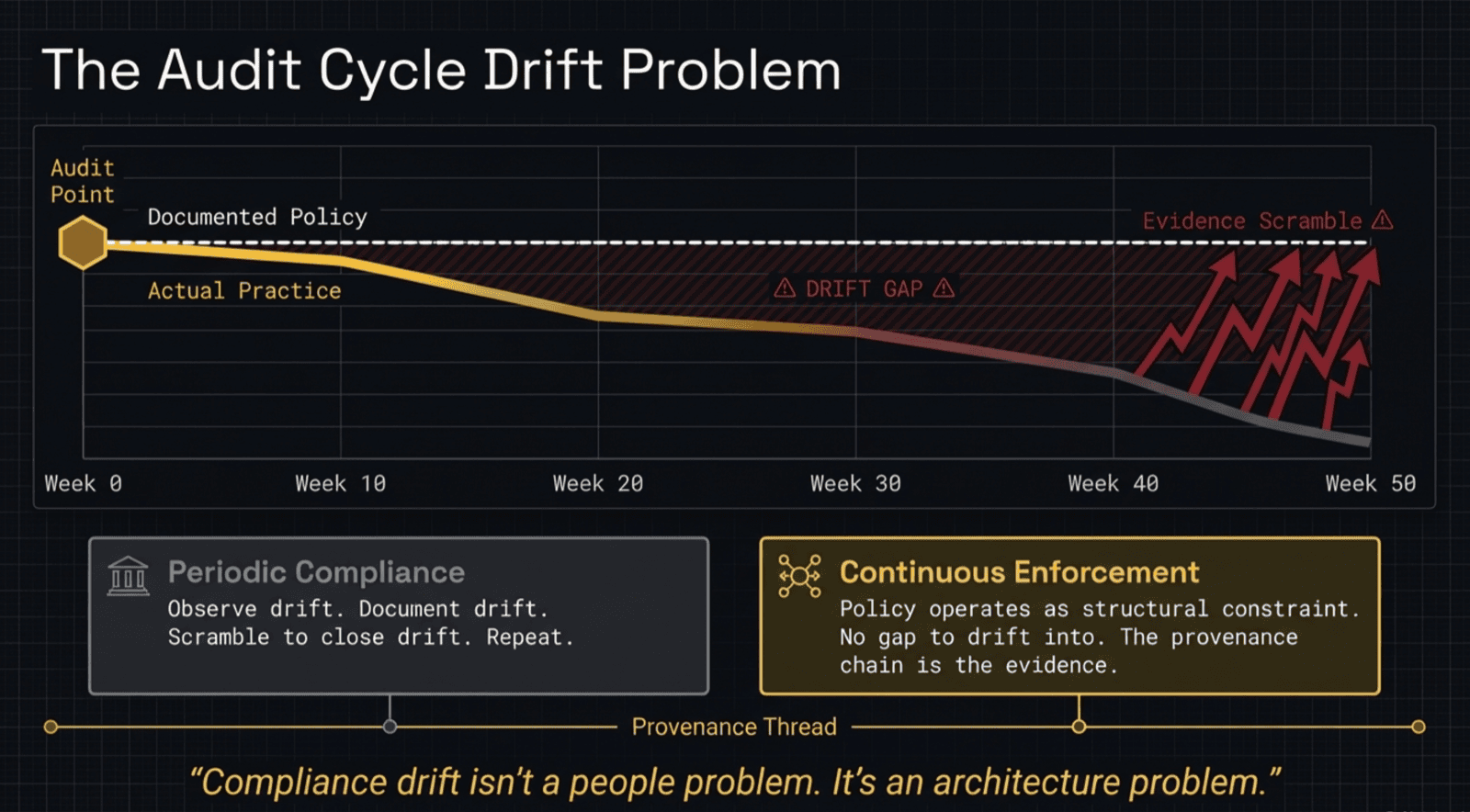
None of these events trigger an alert. None of them appear in a dashboard. None of them are visible until the next audit cycle begins and the scramble starts again. The gap between audits — which is the vast majority of the organization's operational life — is ungoverned space.
This is not a people problem. It is an architecture problem.
Why Static Policy Guarantees Drift
Compliance drift is not caused by negligence. It is caused by a structural mismatch between how organizations operate and how policy is stored.
Organizations operate continuously. Processes change. People move. Systems are updated. Exceptions are made. Every day produces operational decisions that may or may not align with documented policy.
Policy is stored statically. A document in a wiki. A PDF in a compliance repository. A control mapping in a GRC platform. These artifacts have no connection to the operational systems where policy should be enforced. They are reference documents — consulted during audits, ignored between them.
The mismatch is fundamental. A static artifact cannot govern a dynamic system. The artifact describes what the organization intended at the time it was written. The system reflects what the organization actually does right now. The gap between those two things is drift, and it widens every day the policy document sits unchanged.
No amount of better evidence collection solves this on its own, because evidence collection that runs as a separate workstream is structurally disconnected from the policies it's meant to validate. Automated monitoring tools that continuously scan system state — security posture checks, configuration baselines, access reviews — are valuable. They discover drift in real time rather than months later. But they only close the loop if the findings flow back into the policy layer: the misconfiguration triggers remediation, the remediation updates the control, and the closure is documented as evidence. When monitoring and policy operate as one system, evidence is a byproduct of governance. When they operate as parallel systems — one enforcing, one collecting — they can drift apart just as easily as the policy and practice they're meant to keep in sync.
The Periodic Model Is the Problem
The compliance industry's answer to drift has been to increase audit frequency. Continuous monitoring tools check system configurations against baselines. Automated evidence collection reduces the manual effort of audit preparation. Some organizations move from annual to quarterly review cycles.
These are real improvements, and the best of them — continuous monitoring tools that check system configurations against baselines, automated security posture assessments, daily compliance scans — are doing genuine work. An organization that pulls Security Hub findings daily and remediates them in real time has a fundamentally different compliance posture than one that collects screenshots quarterly.
But continuous monitoring alone does not change the fundamental architecture when policy exists in one place, operations happen in another, and monitoring bridges the gap without closing it. Monitoring tells you that something changed. It does not prevent the change from violating policy. And critically, it does not ensure that the policy being monitored is itself current, reviewed, and backed by documented human authority. A monitoring tool that checks configurations against a stale policy is validating compliance against a standard that may no longer reflect organizational intent.
The problem is not the frequency of observation. The problem is whether observation, policy, and enforcement operate as one system or three.
What Continuous Actually Means
Continuous compliance requires a structural change, not a scheduling change.
Policy must be expressed as enforceable constraints — not documents that describe desired behavior, but rules that constrain actual behavior. When a process attempts to violate a policy, the violation is blocked at the point of execution. There is no gap between policy and practice because policy operates within the same systems where practice occurs.
But structural enforcement introduces its own risk: rigidity. If policies can be enforced without documented authority behind them, enforcement becomes arbitrary. Teams route around constraints they don't understand. Exceptions are granted without documentation. The enforcement layer becomes another source of organizational friction rather than a governance mechanism.
This is why enforcement requires provenance. A structurally enforced policy that carries its full decision history — who originated it, who reviewed it, how it matured, why it exists — is transparent enforcement. A structurally enforced policy with no provenance chain is just a system saying "no" with no explanation.
The maturation pipeline ensures that only policies with earned authority reach enforcement status. Provisional corrections are observed, not enforced. Solidified policies with documented human review can be enforced advisorily. Only reinforced policies with complete provenance chains are enforced structurally. The rigor of enforcement is proportional to the documented authority behind the rule.
Between Audits
Compliance drift is an architecture problem, not a discipline problem. Static policy stored separately from operational systems will always drift, regardless of how frequently it is reviewed. And evidence collected separately from governance will always risk diverging from it.
Raknor keeps both sides in sync — compliance documentation and procedures evolve together with live corrections and policy enforcement. The monitoring that discovers a finding, the correction that addresses it, and the evidence that documents the closure are one system, not three. The provenance chain proves the authority behind every rule. The operational record proves the rule is active.