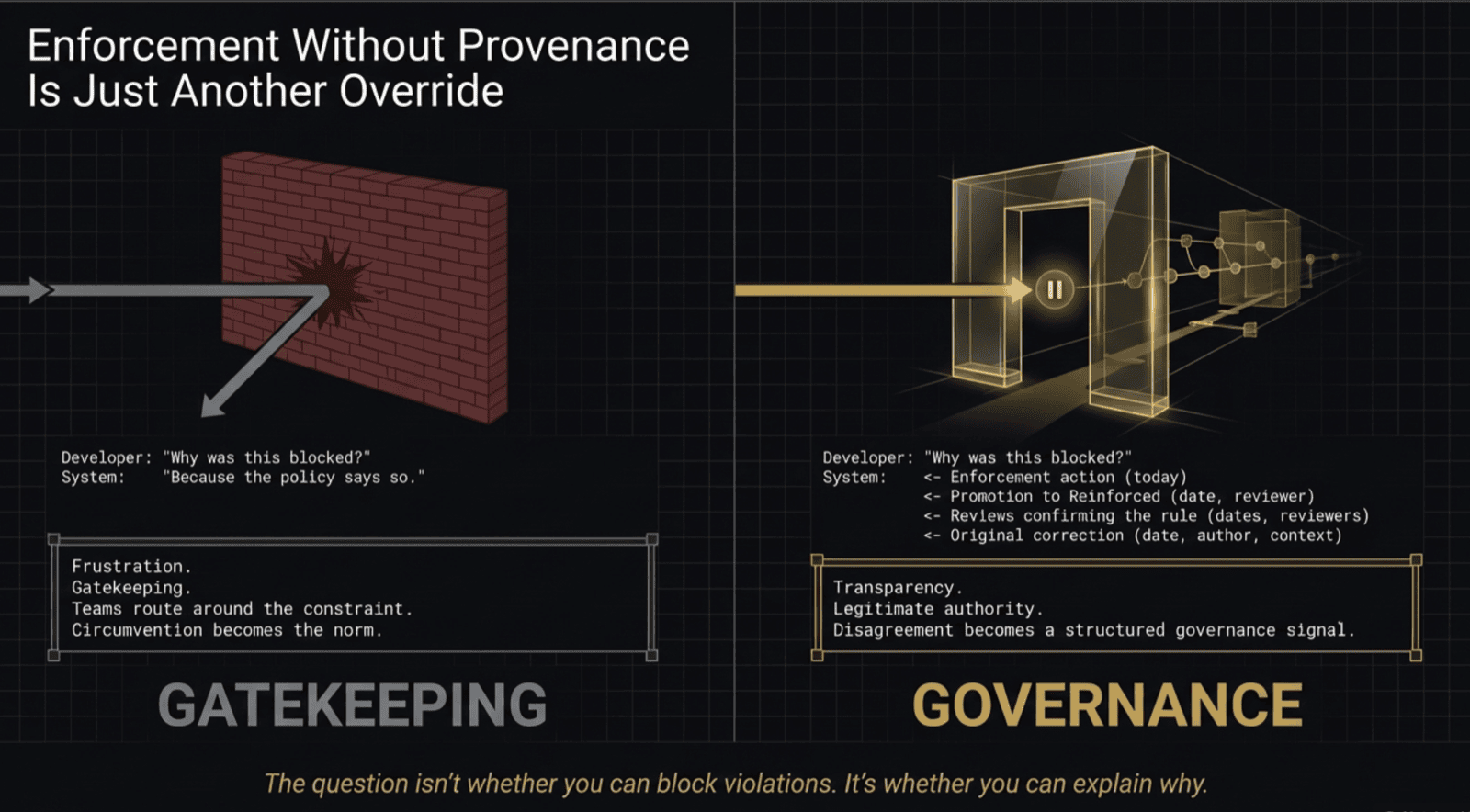
Enforcement Without Provenance Is Just Another Override
Every governance team has heard the complaint.
A developer's deployment is blocked. A workflow is rejected. An automated process hits a constraint and fails. The developer asks the question that every enforcement mechanism must be able to answer: Why was this blocked? Who decided this?
In most organizations, the answer is unsatisfying. "Because the policy says so." "Because the compliance team configured it." "Because the framework requires this control." These answers establish that a rule exists. They do not establish that the rule has authority.
The developer's frustration is legitimate. If you cannot explain why a rule exists — who originated it, what problem it solved, who reviewed it, and how it earned enforcement status — then your enforcement is indistinguishable from arbitrary restriction. You have not governed a behavior. You have obstructed it.
This is the difference between governance and gatekeeping. And it hinges entirely on whether enforcement carries provenance.
The Legitimacy Problem
Enforcement without provenance has a legitimacy problem that compounds over time.
The first time a rule blocks something unexpectedly, the team investigates. They find the rule, accept the explanation, and move on. The second time, they investigate with less patience. By the fifth time, they stop investigating and start routing around the constraint — finding exceptions, escalation paths, or alternative workflows that avoid the enforcement layer entirely.
This is not defiance. It is a rational response to an enforcement system that cannot justify its own decisions. When the cost of complying with a rule exceeds the team's confidence that the rule is correct, non-compliance becomes the default. And the governance team has no counter-argument, because the provenance that would justify the rule does not exist.
The result is an enforcement layer that is simultaneously too rigid (blocking legitimate work) and too permeable (routinely circumvented). Teams that can route around constraints do so. Teams that cannot route around them absorb the friction. Neither outcome is governance.
What Provenance-Backed Enforcement Looks Like
When a Raknor-enforced rule blocks an action, the enforcement carries its own justification.
The blocked action links to the rule. The rule links to the promotion decision that gave it enforcement status — who promoted it, when, and what evidence supported the decision. The promotion links to the reviews that confirmed the rule across multiple contexts. The reviews link to the original correction — the specific moment when someone with domain knowledge identified a deviation and articulated the correct behavior.
Every enforcement action carries the full chain. A developer whose deployment is blocked can trace the chain in seconds: this rule exists because a senior architect identified this pattern as a security risk on a specific date, the correction was confirmed by the security team and the platform engineering lead in subsequent reviews, and it was promoted to reinforced status after six weeks of sustained stability with no challenges.
This changes the conversation entirely. The developer is no longer arguing against an opaque system. They are evaluating documented organizational judgment. They may still disagree — and that disagreement is itself a valuable governance signal that feeds back into the correction pipeline — but the enforcement has legitimacy because its authority is traceable.
Override With a Trail
Provenance-backed enforcement also changes how exceptions work.
In an opaque enforcement system, exceptions are granted through escalation. Someone with sufficient authority approves the override, and the blocked action proceeds. The exception may or may not be documented. Even if documented, it is disconnected from the rule it overrides — the exception lives in a ticket system, the rule lives in a policy store, and the relationship between them is implicit at best.
In a provenance-backed system, an exception is a governance event. It is recorded against the rule's provenance chain. The exception documents who approved it, why, and whether it is permanent or time-bounded. If the same exception is granted repeatedly, the pattern becomes visible — and becomes a candidate for a new correction that modifies the original rule.
Exceptions do not weaken provenance-backed enforcement. They strengthen it. Every exception adds information to the provenance chain. Over time, the chain reflects not just why the rule exists, but also where it has been challenged, where exceptions were necessary, and how the organization's understanding of the rule has evolved.
The Question That Matters
The question is not whether you can block violations. Any system with a deny list can block violations.
The question is whether you can explain why. Whether every enforcement action carries the documented human authority that makes it legitimate. Whether the person affected by the enforcement can trace the decision chain from the block all the way back to the correction that originated the rule.
Enforcement without that chain is just a system saying "no" with extra steps.
Every Raknor enforcement action carries its full provenance chain — from the correction that originated the rule to the human decisions that gave it authority.