Your Policy Has No Chain of Custody
Ask your compliance team a simple question: Show me the decision history behind this control.
Not the policy document. Not the framework mapping. The decision history — who created this rule, what correction prompted it, who reviewed it, and whether anyone has confirmed it still applies.
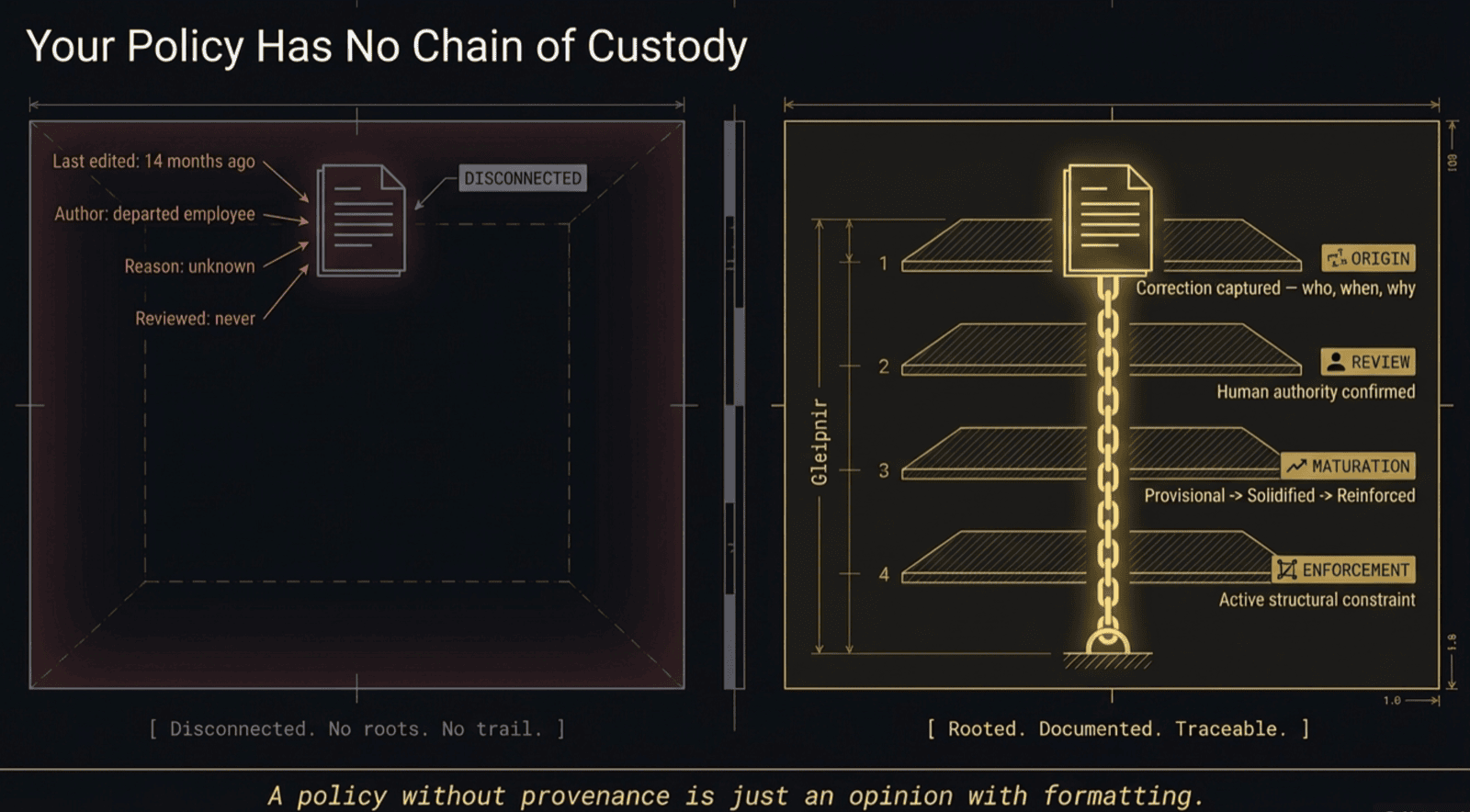
In almost every organization, the answer is silence. The policy exists. It lives in a wiki page or a PDF in SharePoint. It was last edited fourteen months ago by someone who has since left the company. There is no record of why the rule was written. There is no record of what problem it solved. There is no record of any human reviewing it since it was created.
This is the state of organizational policy in 2026. And it is architecturally incapable of surviving an auditor who asks the right question.
The Document Is Not the Evidence
Compliance tooling has spent a decade getting better at generating policy documents. Templates are more comprehensive. Framework mappings are more complete. Evidence collection is more automated. The entire industry has optimized for one thing: proving that a policy exists.
But existence is not authority.
A policy document proves that someone, at some point, wrote down a rule. It does not prove that the rule was arrived at through deliberate human judgment. It does not prove that the rule has been reviewed against current operational reality. It does not prove that anyone with authority decided this rule should be enforced.
An auditor examining a SOC 2 control can verify that the policy document exists and that it maps to the relevant trust service criteria. What they cannot verify — because no tool in the compliance stack records it — is the chain of human decisions that produced the policy and the chain of human reviews that confirmed it remains valid.
This gap is not a documentation problem. It is a governance problem. And no amount of better evidence collection will close it, because evidence collection operates on policy documents, not on the decision history behind them.
What a Chain of Custody Looks Like
A policy with a chain of custody answers every question an auditor should be asking:
Origin. This rule exists because on a specific date, a specific person identified that work was being done incorrectly and corrected it. The correction was captured with attribution — not as a ticket that got closed, but as the origin of a governance artifact.
Review. The correction was reviewed by a human with authority over the relevant domain. The reviewer confirmed that the correction reflects organizational intent, not just one person's preference. The review decision is documented.
Maturation. The rule progressed through documented stages. It started as provisional — a single correction, under observation. It became solidified after being confirmed across multiple contexts and promoted by human review. It reached reinforced status after sustained stability and full provenance documentation.
Enforcement. The rule operates as a structural constraint. When a process or behavior violates it, the violation is blocked at the point of execution. The enforcement action is recorded, and the provenance chain is available to anyone who asks why.
At every stage, the chain of custody documents who decided, when they decided, and what evidence supported the decision. The policy document is a byproduct of this chain — not the source of truth.
Why This Matters Now
Two forces are converging that make policy provenance urgent rather than aspirational.
The first is regulatory pressure. Frameworks are moving from "do you have a policy?" to "prove your policy is effective." SOC 2's trust service criteria, GDPR's accountability principle, and the FCA's Senior Managers Regime all share a common thread: demonstrating that governance is active, not declarative. A policy document with no decision history behind it fails this test.
The second is AI-assisted operations. When agents and automated workflows execute organizational processes, the policy governing their behavior must be traceable to human authority. An agent operating under a rule that nobody can trace back to a human decision is ungoverned by definition — regardless of how many policy documents surround it. The provenance chain is what connects automated enforcement to human judgment.
Organizations that cannot produce a chain of custody behind their policies are operating on trust — trust that the rules are correct, trust that someone reviewed them, trust that enforcement reflects organizational intent. Between audits, that trust is unverified. And unverified trust is where compliance failures accumulate.
The Structural Answer
A policy without provenance is just an opinion with formatting.
Raknor maintains the chain of custody behind every organizational policy — from the correction that originated it to the human review that promoted it to the enforcement that proves it is active. The provenance chain is the audit artifact.